At the university, we did go through physical hardware attacks, like USB keyloggers or getting data from frozen memory sticks and cryptographic keys from smartcards. But as I am finishing my master’s in cybersecurity management, I realized that something has been missing – the actual means of “getting physical.”
You see, In the US, there is a large number of companies carrying out audits that include physical pen-testing. Some of the names involved are relatively famous, like Chris Nickerson or Deviant Ollam. These guys will try to use any means of getting to your facility and then help you improve its security. Meanwhile, in Czech(o)Slovakia, I know of only one company that does this all-around red-teaming, and they told me that the demand and awareness are next to zero here. And this lack of awareness is apparently projecting into the education at my faculty.
Well, having a degree in cybersecurity management and having no clue about the physical security of the infrastructure implies kind of a bummer.
So I decided to do something about it. And the first part was to get the attention of the faculty staff in some way – making a master key to the building. Although I did violate all the locksport principles of decency, a subsequent discussion with several of our university lawyers confirmed that I did so Legally. This attack has been theorized before, but you will struggle to find the actual large-scale example of it anywhere. So, here we come.
Prerequisites
The basic principle can apply to all master keying systems using different methods. However, we will talk about the classic pin tumbler locks that everybody knows. These, even though being replaced by “better” mechanisms, are still the most popular type in either the residential and institutional buildings. Now, starting the attack with zero knowledge is possible, and I might write something about that later. However, in this case, it was a privilege escalation attack, meaning that I already had a key and authorized access to a particular office in the business sector of the faculty. So what did I need to do to create my master key?
Getting to know the system
Every locking system is defined by a bunch of numbers – the distances and sizes of parts of the key and the semantics of the bitting code. In the locksmithing industry, these numbers are structured in so-called cards – named by the physical cards a locksmith had to insert into his cutting machine to cut a key by code. Nowadays, these machines are fully electronic, but the name “card” is still being used.
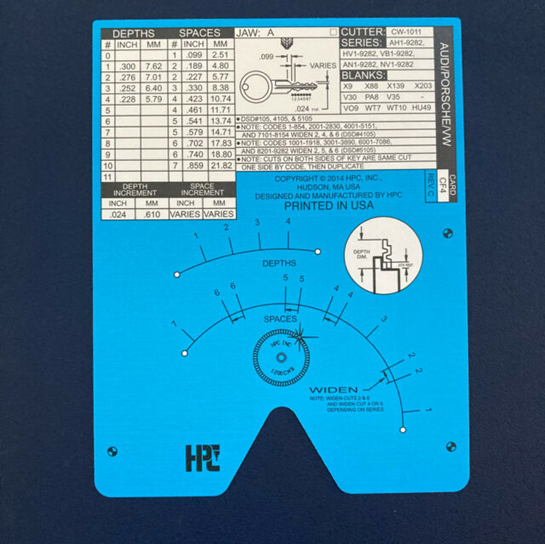

To create a fully functional key, you need to know these values. Namely, you need to know the length of the blade, the position of each cut, and the possible depths of each cut. Then, the only missing information is an actual bitting – the number of n digits, where n is the number of pins in the system.
To check which system you use, you need access to this information. And probably the best way is to use the InstaCode software. You can easily confirm the system by measuring your key with a caliper.
My faculty uses EVVA’s (formerly GUARD) CPS, also marketed under various other names. It is also among the most used locking systems in multiple institutions in the Czech Republic. This system shares these values with most systems by the same Austrian company, so these are united under one single “card.” Because Silca is probably the most important supplier of the key machines in this country, I will use their numbering, which is quite interestingly, a biblical 666 in this case.
Finding working combinations
The theory now goes like this – get a bunch of blank keys and cut them according to your existing key – with always leaving one position uncut. Then, for each key, cut that position bit by bit and try it in your lock every time. Notice that while doing that, you will recreate your original key from every blank for a while – therefore, if its bitting doesn’t work, you are doing something wrong.
However, if the key works while it does not have the same bitting, you have just discovered a new position – a master pin at the corresponding position.
But, there is an apparent snag in the process – the key blank. It is often quite hard to get the blank you need – we will get to that in a while – but for this method, a piece of plastic is a great replacement. I use plastic made by the Chinese company HUK for slammed door opening. It is sturdy yet flexible, so the profile of the lock does not quite matter.
In the video, you can see how to make the mock key from the plastic and how to cut it with the printable “cards” and a 30 USD device – Lishi Key Cutter – with ease. I did create my own “card” for this cutter which can be found here.
Another video shows one of the correct combinations successfully turning the core. Note that the turning tool has a PVC coating so that it does not leave any marks.
Let’s say we have now found all the combinations. How can we tell which one is of the master key? Here, a knowledge of the system helps quite a lot. For that, we need to talk about the profiles.
Getting the proper key blank
Manufacturing key blanks for various locks has become a great business, and companies like Silca and JMA try to cover the whole market. This way, your local locksmith can keep ties to just one of the companies and be capable of dealing with the overwhelming majority of all keys on the market.
However, copy protection can’t work this way. Your “security card” can provide at least some security only if all the locksmiths are bound by an agreement with the original lock manufacturer. That is impossible if the blanks are being distributed freely and the “cards” are no secret. While trying to keep the “cards” secret is quite foolish (anyone would deduce these from a bunch of keys or locks,) restricting the access to key blanks might be somewhat effective. However, with classic pin tumblers this still is not very effective as anyone can buy blanks without profiles that can be hand-filed to the correct profile. There is also a machine, called NETMILL, that can recreate any profile into these blanks automatically. German EasyEntrie is another quite interesting machine.
The most effective way is to create a novel locking mechanism with a key and patent it. This way, the manufacturer has a de jure control over these key blanks as any knock-offs would automatically infringe the patent. Also, if a locksmith who wishes to use these blanks has to agree on specific terms – for example, that he will only make a copy if the customer has a valid security card.
Contrary to common belief, a specific “profile” is not considered novel. To get the patent, you need to introduce something new to the market. A great example is an MCS system from the same company or a beloved Abloy Protec 2.
However, with the CPS, EVVA somehow patented a… key? Let’s take a look at the European Patent no. 1862615. It is a strangely named “Key,” but the resulting keys seem to be no different from the keys we all know. The patent actually introduces a profile system – a base shape from which some combination of triangles can be cut. This way, you can create a system that makes it impossible to insert an incorrect key into a lock.
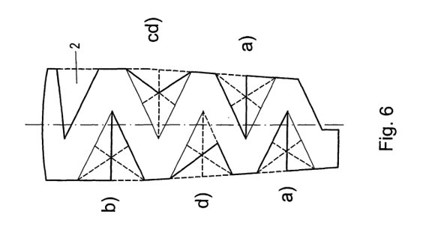
For us, this has a few consequences; First of all, we know how the blank of a master key looks like: it is the base shape with all the triangles cut, and logically, this will work with all the locks in any system that uses this patent. So in the worst-case scenario, we can use the NETMILL blank and slowly hand-file the profile.
But we know that the patent claims only the profile system itself – making it possible to produce a blank key, somewhat similar to the “full cut” profile, without violating the patent. With the number of various lock manufacturers out there, what is the chance that we can find a freely distributed blank that would work as the system? Well, very high. Look at this video:
What you just saw was Silca’s Optika machine in action. It can measure the key’s bitting and profile accurately. These measurements can then be used in the NETMILL machine or compared with the profile database. In this case, a TN36R blank initially intended for the Slovenian Titan K6 locks pops up as a possible alternative. Indeed, it worked with the lock. When you compare its profile with the drawing from the patent, there is no wonder why.
Getting the right bitting
The patent also tells us something about the resulting systems. Larger systems have several levels of access – having “group keys” under the master key, which would typically increase the number of master wafers in these locks. At the same time, it is common knowledge that using master wafers significantly reduces the protection introduced by security pins. EVVA has decided to use its patented profile system to distinguish group keys from the master key – with both actually having the same bitting. The only difference between various group keys and the master key is that it is impossible to insert them into another group’s lock. First, it means that you already have the right bitting if you happen to have access to some group key. But it also makes deducing from our combinations easier;
Let’s say that the bitting of your original key was 12345 and that you have found that 3 on the second position, 4 on the third position and 5 on the fourth position also work. It only has the economic sense to introduce these new combinations if they are used. And because we know that the group keys and the master key have the same bitting, we can be almost 100% sure that the master key has a bitting of 13455. You can always cut another plastic key with this combination and try it in other locks if you’re not sure.
Creating a key
Now we have everything we need – the “card,” the bitting, and the blank. Now you can buy the blank key and hand-file the bitting. But why not try to ask a local locksmith to create it for you?
So I came to the locksmith and told them that I need to cut the found bitting on the Silca TN36R blank, with the cutting machine set to Silca card 666. And although they were staring at me for a while, they did it. Why? There was absolutely nothing that would stop them – The blank is freely distributed, the card is not restricted (as it is being used even with keys that officially do not need a security card for copying), and the bitting is just a piece of information to insert into a machine.
Aftermath
I have shown the key to one of our professors, and he showed it to the whole faculty management. They have decided to pick some of the most important rooms and exclude them from the system. But the professor considered my claim – that everything I did was absolutely legal – a mere euphemism. So he called for a meeting with a bunch of lawyers from our university. And they have confirmed that.
How come? The situation is strange as the local law is quite the opposite of what’s in the US. In Europe, if you get unauthorized access to anything that could be qualified as a “computer system,” even accidentally, you can end up in jail. Your intentions of doing so are not of interest to anyone. On the other hand, it is not considered a crime if you trespass or commit burglary that causes low damages. And nobody can just shot you while doing so.
The only thing that is still puzzling me is the absence of demand for physical security audits in Czech(o)Slovakia. Because apparently, it is much easier to hack the physical world here. I hope that this will change and that this blog post might help a little.
Anyway, the professor agreed that I can for now at least do a lecture about this very small part of physical security, with the possibility of extending that to a full course at the faculty of Informatics of Masaryk University. This is it:
